New Pluralsight Course: Communicating and Documenting Security Incidents
New Pluralsight Course: Communicating and Documenting Security Incidents

In April the US bank Sun Trust confirmed they had a data breach, (potential theft from a former employee). Just at the end of May, BleepingComputer.com reported that Coca Cola had a similar incident when about 8,000 individual's information was on a hard drive in the pocession of a former employee. Both organisations had to communicate these security incidents to the appropriate supervisory authorities and also the affected data subjects (employees who’s data was taken).
What do these two incidents have in common? Well on Friday last my latest Pluralsight course was published which means I now have Pluralsight courses heavily related to these incidents:
Let’s talk about Communicating and Documenting Security Incidents for a moment.
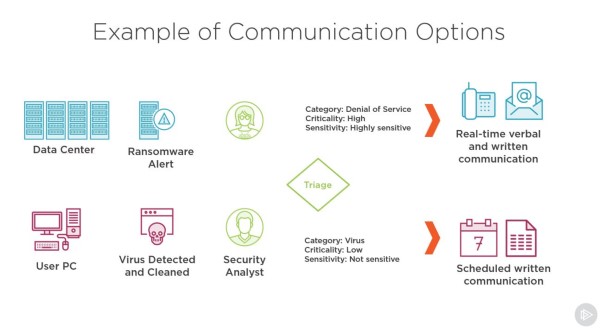
Any organisation responding to a security incident is communicating and documenting the incident. With the arrival of GDPR (the General Data Protection Regulation) and other mandatory notification laws, the task of communicating security incidents has become far more formal.
In this course I take you through this subject starting with what we mean when we say “communicating and documenting” security incidents. Much of these activities today can be done automatically, however there is significant benefit in skilling up on these activities to help make your incident response more effective.

I take you through the mandatory reporting requirements and look at the official documentation of security incidents, starting with ticket creation all the way through to the official ICO data breach template.
I also share some techniques you can use to apply to your process.