Stop playing kiddie football and focus on the basics

Learn from others' incidents:
On June 1st Microsoft published an analysis of the Hacking Team Breach in their Cyber Trust Blog. It’s a really good read, which you can find here, for anyone who wants to learn some lessons on defending their network.
Recently I published by first Pluralsight Course on Information Security and thought it would be interesting to assess the controls listed in the ISO27001 standard to see if they would have helped reduce the risk in the Hacking Team Breach scenario, at least in theory. What I found was relief and reassuring, in this age of hyper-reaction by media and industry to cybercrime stories. Let me explain.
I took the lessons from this analysis and determined if the Hacking Team had implemented the ISO27001:2013 controls, would it have helped reduce the risk of a breach. Some may think the ISO27001 standard for information security is outdated, and past its usefulness, especially given the word “Internet” doesn’t even appear in the standard’s text, however I would take a much different view. Everything that is in the ISO27001 standard is what you should be doing as a minimum baseline when trying to protect your organisation. All the answers lie within the standard, you just need to recognise today’s variants and map these back to the standard.
What industry leaders think:
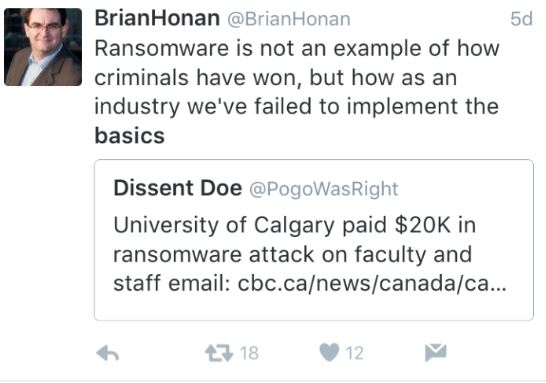
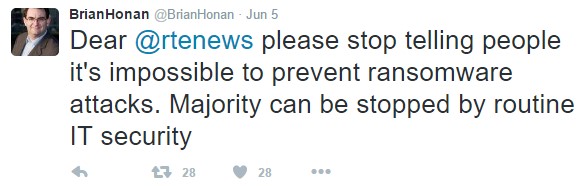
For example, at InfoSecurity Europe 2016, Brian Honan, who took his place in the event’s hall of fame, urged companies to focus on getting the basics right, and not getting repeatedly distracted with running to the latest media driven cybersecurity scare. You can read the write up here.
Dublin-based Honan also complained that the industry is too fixated on hyping the latest major threats – arguing that ransom-ware is ultimately just another form of malware, albeit a particularly aggressive one.
First, they should instead concentrate on getting the basics right and they’ll eliminate a large percentage of risk.
“If we keep responding to the latest threats, we’ll never have time to get the basics right," Honan claimed.
I do agree with Brian, and the reaction to recent incidents resonates of a kiddie’s football team, with everyone chasing the ball but no one being concerned about the lack of structure or organisation to ensure all the basics are covered.
And here is another example of the media taking the ball and running with it.
Analysis
The analysis by Microsoft called out 8 key tactics, techniques and procedures (TTPs), let’s see if ISO27001, if implemented would have reduced some of these risk areas.
TTP1: External Network Reconnaissance.
Clause A13.1.3 refers to Segregation in Networks.
TTP2: Internal Network Access
Section A.9.1.2 deals with Access control for the network.
TTP3: Internal Network Reconnaissance
Clause A12.4.3 refers to monitoring Operator logs.
TTP4: Compromised Credentials
See section A9.2 which covers a whole list of controls around User Access Management.
TTP5: Domain Admin Compromised Credentials
Section A9.2.3 refers to the management of privileged access rights. Other relates clauses in this section refer to reviewing access rights, and adequate user account provisioning. Clause A12.4.3 refers to monitoring Administrator logs.
TTP6: Domain Dominance
Once the attacker was able to gain Domain access they were springboard their access using many resources available to them.
TTP7: Lateral Movement
Clause A13.1.3 refers to Segregation in Networks.
TTP8: Exfiltration
There is no explicit control relating to exfiltration however the combination of access control, network segregation and others will address this risk.
Lessons for all us:
So in summary, it’s all there, each of the Tactics, Techniques and Practices that were listed are all there in the ISO27001 standard, you just need to recognise them as the standard’s text won’t be so explicit to the examples we see in the media. You have the answers. It is only a matter of focus and interpretation to protect your business by applying these controls.
The Minimum baseline is documented, don’t ignore it.
I’m not saying that the ISO27001 standard is all you need to know, but I am saying it is the minimum baseline you should implement to protect your organisation. Of course once you are certified you continue to build and improve your security management system.
Outsource instead of ignore.
Companies can be very busy taking care of business, so it is well worth considering what aspects of your management system you can outsource to a managed service provider. This doesn’t have to be a big bang approach, you can start by getting some of the routine work completed by a trusted third party partner, the most important thing is that ensure you have suitable coverage on the field.
Don’t leave yourself with an open goal, ensure you have the basics covered and then you will be able to deal with the new variants of threat.
Learn more by checking out my Pluralsight course ISO27001: Information Security – the Big Picture